AI Integration Services
Secure API connections, webhook orchestration, and data pipelines that connect AI capabilities to your existing systems — so automation works end-to-end without brittle, undocumented hacks.
Discuss Integration Needs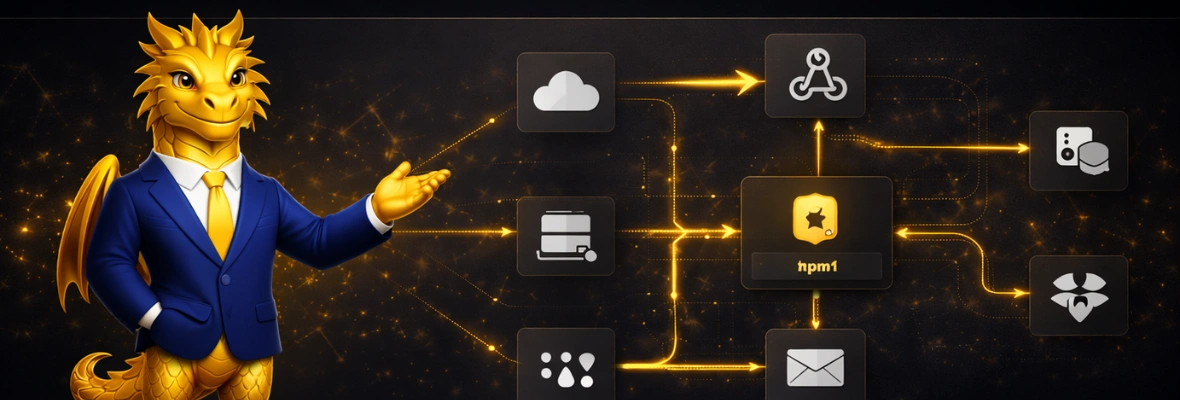
Why Integration Is the Hard Part
AI models are powerful in isolation. But real value comes when AI connects to your CRM, billing system, project tools, and data warehouse. The challenge isn't the AI — it's building integrations that are secure, reliable, and maintainable. That's where most automation projects fail.
Our Integration Approach
Dracau designs integration architectures that prioritize durability: proper authentication flows, rate limiting, error handling, data validation, versioning, and observability. We build integrations that run in production for months without manual intervention — and alert you immediately when something needs attention.
What's Included
Common Integration Scenarios
CRM & Sales Stack
Connect AI to your CRM for automated enrichment, lead scoring, activity logging, and pipeline updates — with data integrity safeguards built in.
AI Model & LLM Integration
Embed LLM capabilities into your workflows with structured prompts, output parsing, fallback handling, and cost monitoring.
Cross-Platform Data Sync
Keep data consistent across tools — billing, project management, analytics, and communication — with real-time or scheduled sync pipelines.
Webhook Orchestration
Receive, validate, route, and process webhook events from external systems with proper queuing, deduplication, and error handling.
AI Integration FAQs
Any system with an API — CRMs (Salesforce, HubSpot), ERPs, databases, billing platforms, communication tools, and AI/ML services. We design custom connectors when standard integrations aren't sufficient.
We build integrations with version awareness and change detection. When upstream APIs change, our monitoring detects the issue and alerts your team before it impacts production workflows.
Security is foundational. We implement proper authentication (OAuth, API keys, certificates), encrypt data in transit, and follow least-privilege access principles for every connection.